Businesses routinely become victims of cyber crimes, and one way to limit exposure is to conduct frequent and thorough IT health checks. Various approaches exist, but certain elements apply to most companies.
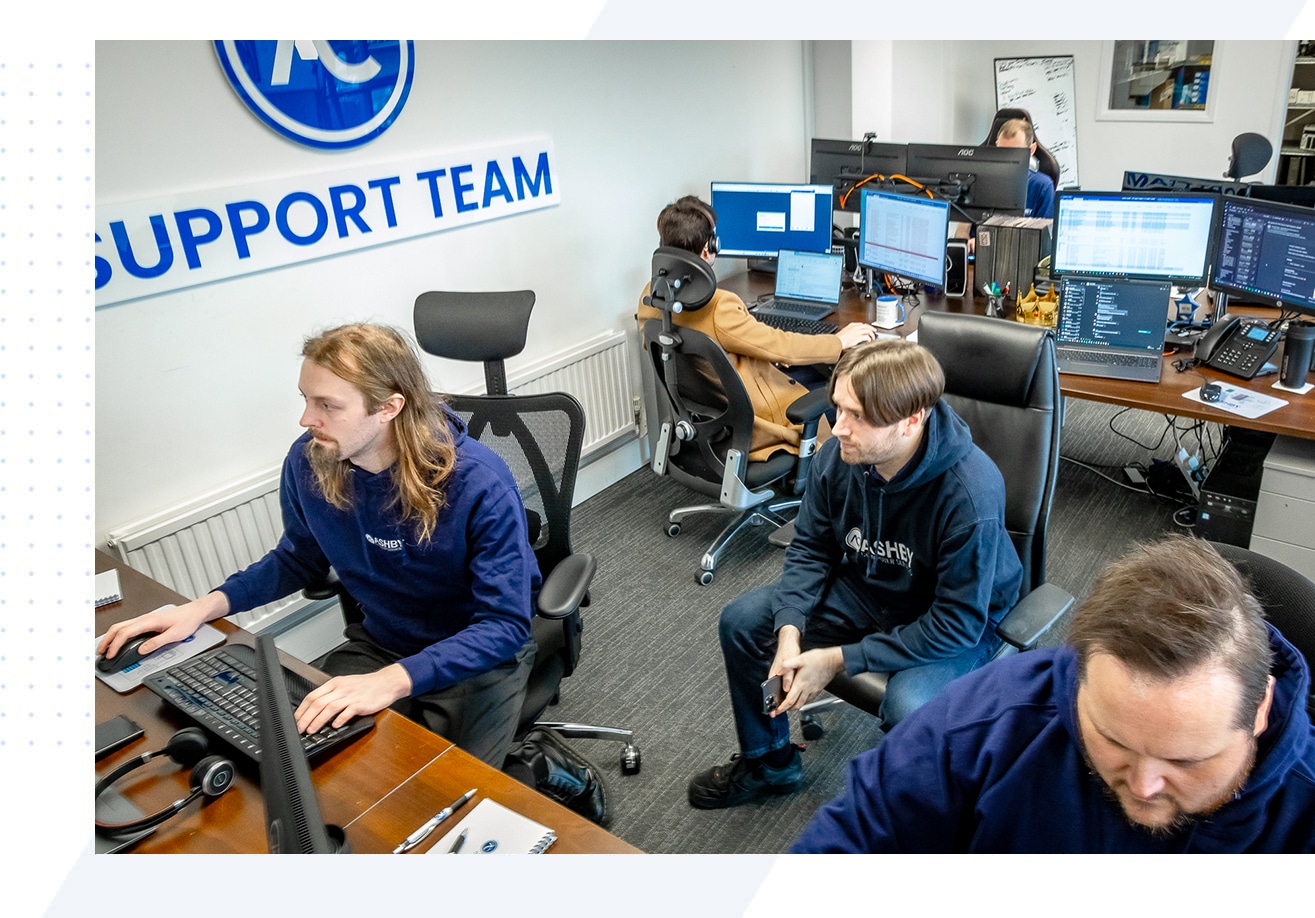
- Identify current concerns
Work with the internal IT staff to gain insight into current issues. Hiring external consultants to either perform initial evaluation or work with the existing IT staff is also an option and can uncover previously missed opportunities for improvement.
- Create/check process maps and documentation
A thorough, clear documentation on setting up the network from scratch is key to ensuring business continuity in case of a data breach or other emergency. The best way to test the usability of documentation is for a new/unfamiliar person to follow it verbatim and see if that produces desired results. Identified documentation shortcomings should be remedied.
- Evaluate
Creating a list of critical areas, such as data backup and monitoring, and then assessing them for possible issues is a good approach. Identifying which areas have the greatest exposure lays out the framework for future risk mitigation and ongoing monitoring.
- Implement and Educate
Compile reports of the findings, then create solutions to address the issues. Areas that require more in-depth assessment should be revisited. The final step of any health check includes a written report of the findings and the suggested action steps that are communicated to the affected users. One potential area for cyber security breach is user error (such as opening phishing emails and getting infected with Cryptolocker), so collaboration with non-IT personnel is crucial.
For more information on how to protect your data and IT infrastructure, contact us or request a Free IT Health Check.